
Facing and mitigating IP address abuse in IPv4 transfer and lease markets
It goes without saying that an increasing number of internet users, devices, and applications correlates with the growing number of vulnerable points and the climbing risk of Internet Protocol (IP) address abuse — an umbrella term that describes all types of cybercrime, including spam, phishing, and malware.
The global scarcity of IP version 4 (IPv4) number resources only aggravates this issue. As IPv4 addresses become increasingly valuable, malicious actors have found ways to take advantage. For example, they can attempt to hijack hundreds of thousands of IPs assigned by Regional Internet Registries (RIRs) and resell them to malicious actors for millions of dollars.
The IP lease market is not immune when it comes to IP abuse, either, as leased IP assets can also be abused. IP resource holders at the IPXO Marketplace can also face spam, phishing, or other fraudulent acts involving their assets. Before we dive deep into leased IP asset abuse statistics, let’s take a closer look at IPv4 transfer market abuse.
IPv4 abuse: Taking advantage of Regional Internet Registries and the transfer market
IPv4 address exhaustion throughout the 2010s influenced the emergence of the transfer market, which has been able to offer a solution for those who need IP resources to scale. However, transferred IPs are not immune to abuse.
Over time, RIRs have developed policies intended to prevent IP space registration issues that can lead to IP abuse. ARIN has also successfully implemented a Fraud Reporting Process that enables community members to report resource abuse, including fraudulent internet number transfers, IP asset hijacking in ARIN’s database, or unauthorized changes to Whois information.
Undeniably, outdated records can become a prime target of IP address hijackers who may exploit dormant IPs for spamming, phishing, or other malicious attacks. Therefore, legacy space holders must be diligent about keeping their records up to date.
In some cases, malicious actors are successful at stealing millions of IPs from RIRs and selling them on the black market. In these cases, companies are automatically stripped of the possibility of acquiring IPv4 addresses they need for legitimate business operations.
On the other hand, malicious actors can exploit the transfer market and RIRs’ waiting lists to obtain IPs legally and then misuse them for spamming, phishing, or spreading malware. In fact, according to research led by Dr. Vasileios Giotsas at Lancaster University, IP addresses are 4 to 25 times more likely to be blacklisted after the transfer. Subsequently, this can lead to a damaged IP reputation.
To facilitate legitimate transfers and prevent transactions in the black market, RIRs are serious about handling resources and recording information. ARIN, for example, contributes by educating legacy IP holders and implementing rigorous resource management policies. Of course, legacy space holders themselves must assume the responsibility of regularly updating Whois information.
ARIN IPv4 resources in the lease market: A deep dive into abuse
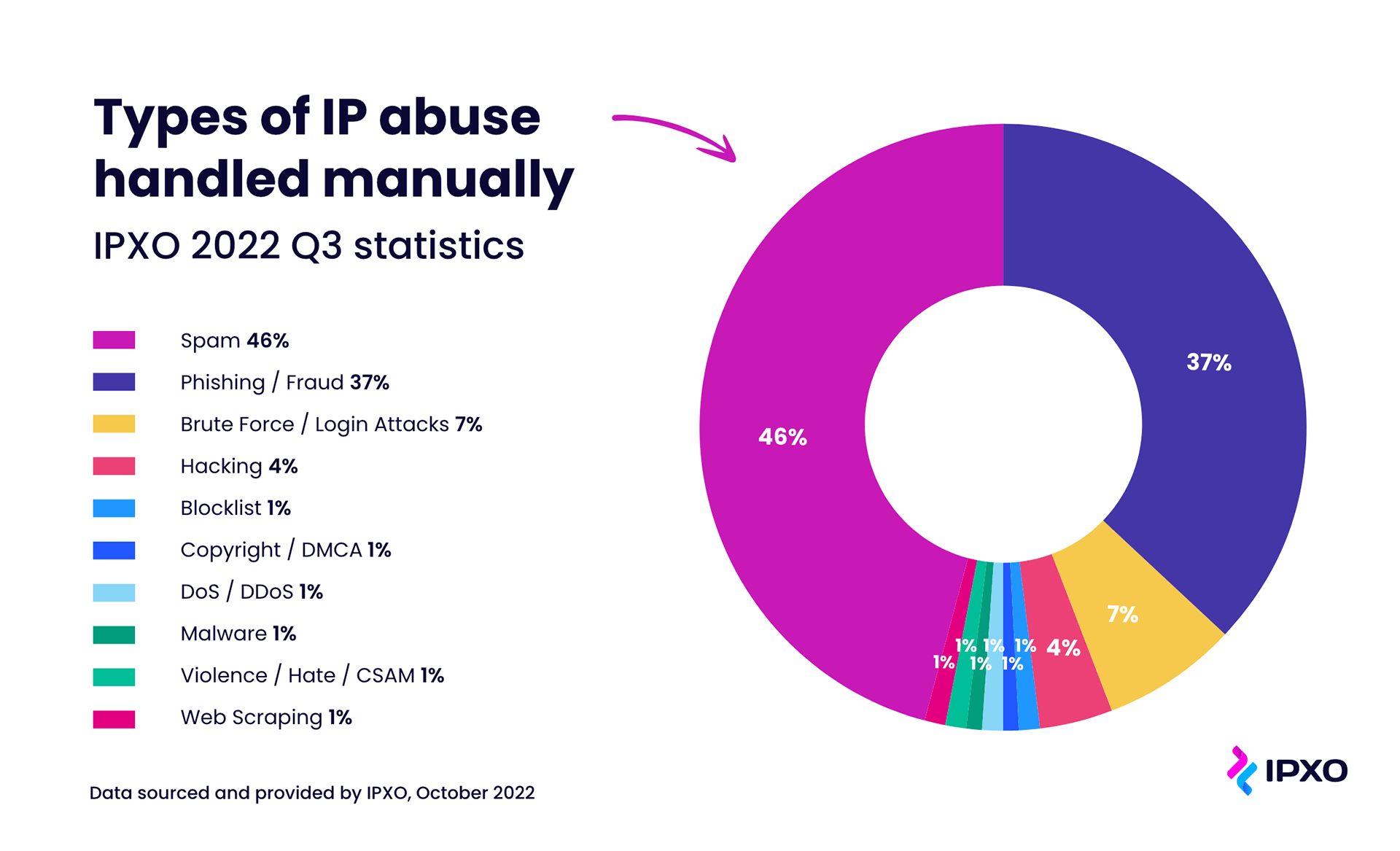
As the first fully automated IP address lease platform, the IPXO Marketplace can offer an interesting perspective into the IP abuse landscape and the common types of abuse. In 2022 Q3, IPXO handled more than 22,000 IP abuse incidents, of which 800 cases were handled manually. Of all abuse cases, 1,340 were linked to ARIN resources — 1,200 handled automatically and 140 manually.
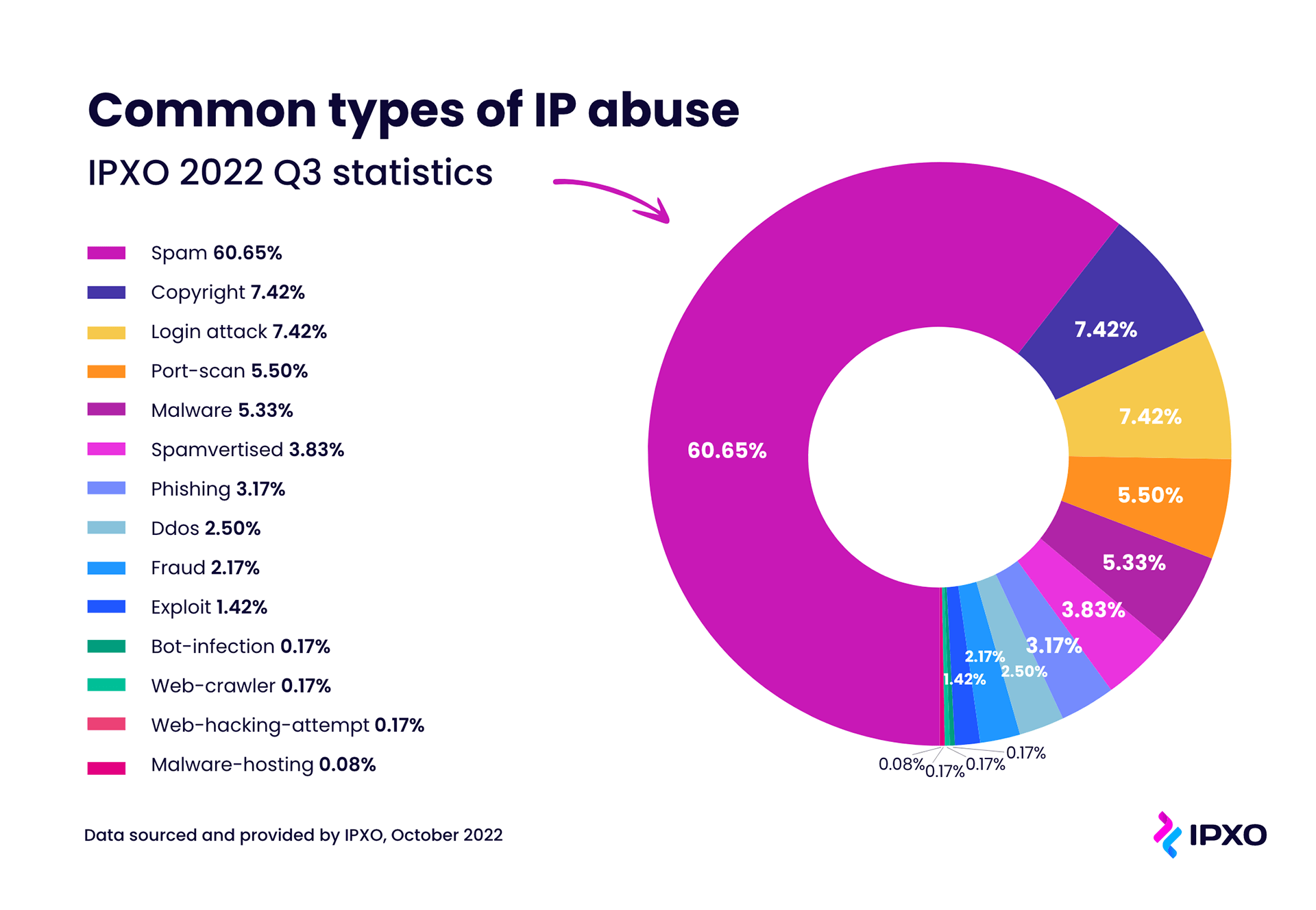
In total, 90% of all abuse incidents linked to ARIN resources were handled automatically, while 10% were handled manually. Spam-related cases required a hands-on approach 46% of the time.
This is not surprising, considering that spam represented the biggest portion — 60.65% — of IP abuse incidents targeting ARIN resources. Copyright incidents and login attacks were the next biggest threats, each linked to 7.42% of all abuse cases.
While some types of IP address abuse are more difficult to handle than others, all types of abuse can negatively affect IP holders who choose to monetize their valuable assets. Therefore, reputable IP lease platforms heavily invest in abuse mitigation and prevention mechanisms, introduce strict know-your-customer (KYC) policies, and provide professional IP reputation monitoring services.
Efficient management tools and policies: The keys to IP abuse mitigation
Overall, IP abuse is a serious issue that must be addressed to ensure a safer and more sustainable use of valuable Internet resources. Fortunately, organizations that allocate and manage IP addresses and those using the assets can change the IP abuse landscape.
RIRs, legacy space holders, and other organizations involved in the IP transfer market can work together to prevent IP address abuse. While internet registries can implement strict transfer policies, IP holders can do their part by introducing proper ownership information management practices. Simultaneously, IP lease service providers can offer vital insights into the abuse landscape to assist both RIRs and IP holders.
Ultimately, while it may be impossible to prevent 100% of IP address abuse incidents, with proper measures we can mitigate them effectively.
Any views, positions, statements, or opinions of a guest blog post are those of the author alone and do not represent those of ARIN. ARIN does not guarantee the accuracy, completeness, or validity of any claims or statements, nor shall ARIN be liable for any representations, omissions, or errors contained in a guest blog post.
Recent blogs categorized under: IPv4
GET THE LATEST!
Sign up to receive the latest news about ARIN and the most pressing issues facing the Internet community.
SIGN ME UP →Blog Categories
Customer Feedback • Elections • Outreach • Internet Governance • IPv6 • Public Policy • Tips • Training • Fellowship Program • RPKI • Caribbean • Grant Program • ARIN Bits • Updates • Guest Post • IPv4 • Security • IRR • Data Accuracy • Business Case for IPv6



